| 1 |
 |
Intro To Pcap Analysis! |
13 years, 5 months |
SecurityAegis |
pcap, pcap analysis, malware, pentesters |
7772 |
None |
| 2 |
 |
Hacktivism, Apple App Store, Vodafone, Facebook - Sophos 90 Sec News - Jan 2011 |
13 years, 5 months |
Sophos |
apple, app store, piracy, malware, wikileaks, anonymous, DDoS, arrest, facebook, privacy, rogue app, vodafone, sophos, sophoslabs, law enforcement |
4517 |
None |
| 3 |
 |
How To Hide Files |
13 years, 4 months |
kassych |
hide, malware, hidden |
4448 |
None |
| 4 |
 |
Nullcon Goa 2011: Chupa Rustam - By Abhijeet Hatekar |
13 years, 2 months |
nullcon |
ip video, hacking, tool, malware, nullcon |
8061 |
1 |
| 5 |
 |
Nullcon Goa 2011: Automatic Program Analysis Using Dynamic Binary Instrumentation - By Sunil Kumar |
13 years, 2 months |
nullcon |
malware, analysis, re, hacking, nullcon, reverse engineering |
7411 |
3 |
| 6 |
 |
Nullcon Goa 2011: No Bullshit, Underground Crime: Traces, Trends Attribution And More - By Fyodor Y |
13 years, 2 months |
nullcon |
hack, underground, IT undercround, cyber crime, intelligence, null, nullcon, exploit, hacking, hacker, fyodor, malware, security, conference, hacking conference, cyber warfare, cyber war |
7408 |
None |
| 7 |
 |
Bad Robots |
13 years, 2 months |
mr_insecure |
malware, analysis, backtrack, day, back-track.de, virus, ida, python |
6296 |
None |
| 8 |
 |
Banking Malware At 25c3 |
13 years, 1 month |
SecurityTube_Bot |
malware, 25c3 |
4564 |
None |
| 9 |
 |
From Badware To Malware: Taming The Malicious Web |
13 years, 1 month |
SecurityTube_Bot |
malware, badware |
4451 |
1 |
| 10 |
 |
Securitytube Live Blackhat: Malware Analysis By Mark Russinovich (Short Clip) |
12 years, 12 months |
SecurityTube_Bot |
blackhat, malware, analysis, mark, russinovich |
6527 |
None |
| 11 |
 |
Malware Goes To The Movies |
12 years, 11 months |
SecurityTube_Bot |
deepsec, malware |
5145 |
None |
| 12 |
 |
Dyi Malware Analysis With Minibis |
12 years, 11 months |
SecurityTube_Bot |
deepsec, malware |
5808 |
1 |
| 13 |
 |
New Research: The "Malware Adoption Lifecycle" |
12 years, 11 months |
Mazoo |
APT, targeted attacks, malware, malware lifecycle, exploit kits. Phoenix, Blackhole |
4680 |
None |
| 14 |
 |
Reverse Engineering The Rsa Malware Attack |
12 years, 10 months |
SecurityTube_Bot |
rsa, malware |
5147 |
1 |
| 15 |
 |
Malware Attribution: Tracking Cyber Spies And Digital Criminals |
12 years, 10 months |
SecurityTube_Bot |
malware, spies, attribution |
4447 |
4 |
| 16 |
 |
Joomla Plugin Sql Injection + Php Malware |
12 years, 9 months |
SecurityObscurity |
joomla plugin, blind sql injection, php, malware, exploit |
6875 |
3 |
| 17 |
 |
Oscommerce Malware Infection + Internet Explorer Exploit |
12 years, 9 months |
SecurityObscurity |
oscommerce, exploit, windows xp, internet explorer 6, remote code execution, malware, metasploit |
5429 |
None |
| 18 |
 |
Fighting Computer Malware At Hacktivity 2011 |
12 years, 8 months |
SecurityTube_Bot |
hacktivity, malware |
4608 |
None |
| 19 |
 |
Alternate Data Streams-- An Oldie But A Goodie |
12 years, 7 months |
sketchymoose |
ADS, alternate data streams, malware, forensics, streams, System Internals |
4843 |
1 |
| 20 |
 |
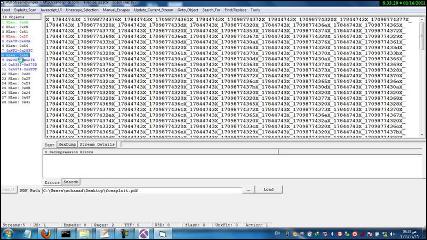
Pdf Analysis Using Pdf Stream Dumper |
12 years, 7 months |
sketchymoose |
PDF stream dumper, CaptureBAT, contagio, PDF analysis, forensics, malware, REMnux, Didier Stevens |
8067 |
None |
| 21 |
 |
Clase 6 Curso Backtrack 5 Online |
12 years, 7 months |
p0pc0rninj4 |
botnet, malware, rootkit detector, rkhunter, defensa, spanish |
4499 |
None |
| 22 |
 |
Foxit Reader Pdf Exploit + Windows 7 Backdoor |
12 years, 7 months |
SecurityObscurity |
backdoor, exploit, foxit, hack, malware, metasploit, pdf, reader, phishing, SET, social engineering toolkit, windows 7, backbox |
9250 |
1 |
| 23 |
 |
Clubhack 2011 - Hacking Your Droid - Part 1 |
12 years, 5 months |
ClubHack |
clubhack, hacking android, reverse engineering, malware, android security model, DVM, GEINIMI, Dreamdroid, mobile penetration testing |
8321 |
None |
| 24 |
 |
Clubhack 2011 - Hacking Your Droid - Part 2 |
12 years, 5 months |
ClubHack |
clubhack, hacking android, reverse engineering, malware, android security model, DVM, GEINIMI, Dreamdroid, mobile penetration testing |
6632 |
None |
| 25 |
 |
Clubhack 2011 - Hacking Your Droid - Part 3 |
12 years, 5 months |
ClubHack |
clubhack, hacking android, reverse engineering, malware, android security model, DVM, GEINIMI, Dreamdroid, mobile penetration testing |
6553 |
None |
| 26 |
 |
Defconjp #Dcg893 2012-2 How Web Vulnerabilities Accelerate Malware Fast Mass Infection |
12 years, 4 months |
unixfreaxjp |
OCJP, malware, japan, android, fraud, CMS, spyware, disclosure |
3793 |
None |
| 27 |
 |
The Hidden Threats Behind Web Banners |
12 years, 3 months |
TalkTechToMe |
malware, web security, network security, hacking |
5033 |
2 |
| 28 |
 |
5 Minute Malware Analysis |
12 years, 2 months |
Securitytube_Poster |
malware, analysis, virus, botnet, linux |
5163 |
2 |
| 29 |
 |
Reverse Engineering 101 |
12 years, 2 months |
Securitytube_Poster |
Reverse Engineering, cracking, system, talks, virus, malware |
7782 |
None |
| 30 |
 |
Stuxnet (Hungry Beast) |
12 years, 2 months |
Securitytube_Poster |
stuxnet, malware, virus, infection, hacking |
5403 |
1 |
| 31 |
 |
Six Million Oscommerce Pages Infected--Malware Analysis Of Incident |
12 years, 2 months |
Securitytube_Poster |
malware, analysis, attack |
3928 |
None |
| 32 |
 |
Tdl4 Rootkit - Being Used As A Proxy |
12 years, 2 months |
Securitytube_Poster |
rootkit, proxy, malware |
4446 |
1 |
| 33 |
 |
Malware Makers Targeting Android Phones |
12 years, 2 months |
Securitytube_Poster |
malware, android, phones, virus |
4039 |
1 |
| 34 |
 |
Persistent Threats |
12 years, 2 months |
Securitytube_Poster |
stuxnet, malware, virus, threats |
3874 |
3 |
| 35 |
 |
Hpw2012 - Countering The Removable Device Threat With Usb Honeypots |
12 years, 2 months |
Securitytube_Poster |
malware, usb, honeypots |
3694 |
None |
| 36 |
 |
Debug Tdl4 Bootkit Part Via Ida + Bochs |
12 years, 1 month |
Ashish_st |
tdl4, bootkit, malware, virus |
5114 |
1 |
| 37 |
 |
Bit9 Stops Advanced Malware 'Flame' |
12 years, 1 month |
Ashish_st |
bit9, malware, virus, flame |
4357 |
2 |
| 38 |
 |
Kaspersky Lab's Research On Mac Malware Outbreaks: Sabpub Trojan And Flashback/Flashfake Botnet |
12 years, 1 month |
jibesh_st |
Trojan, Flashbac, malware |
3875 |
2 |
| 39 |
 |
Microsoft Malware Protection Center (Mmpc) Threat Research And Response |
12 years, 1 month |
jibesh_st |
malware, microsoft |
4428 |
2 |
| 40 |
 |
I Know Your Password |
12 years, 1 month |
jibesh_st |
password, flame, malware |
4755 |
2 |
| 41 |
 |
What Is Flame Malware ? (Cyber Espionage) |
12 years, 1 month |
tinitee |
Flame, malware, virus, hacking, cyber |
4521 |
5 |
| 42 |
 |
Malware And Social Engineering Attacks |
12 years, 1 month |
Alone |
malware, botnet, trojan, hacking, hack, worm |
4604 |
5 |
| 43 |
 |
Malvertising And Mobile Malware Madness |
12 years |
Ronaldo |
hacking, malware, phone, android |
3871 |
None |
| 44 |
 |
Iranian Experts Warn About Cyber Warfare Threats |
12 years |
Alone |
flame, malware, cyber-war, hacking, hack |
4666 |
3 |
| 45 |
 |
Flame Malware How It Works And Causes Havoc |
12 years |
Keyronie |
flame, malware, hacking, cyber-war, hack |
5350 |
4 |
| 46 |
 |
Flame: Trying To Unravel The Mystery Of Spying Malware |
12 years |
Keyronie |
flame, malware, hacking, cyber-war, hack |
4550 |
3 |
| 47 |
 |
Mobile Cyber Security |
12 years |
J0rdan |
hacking, threat, malware, smart-phone |
4048 |
None |
| 48 |
 |
Dumping Polymorphic Malware From Memory |
12 years |
John-Nash |
virus, malware, polymorphism |
4513 |
1 |
| 49 |
 |
Tektip Ep1 - Basic Dynamic Malware Analysis |
12 years |
1aN0rmus |
malware, malware analysis, basic, dynamic, tutorial, apatedns |
6451 |
1 |
| 50 |
 |
Reversing And Malware Analysis - Basic Malware Analysis |
12 years |
Vulnerable |
reverse-engineering, hacking, hack, malware |
6242 |
1 |
| 51 |
 |
Advanced Malware Analysis |
12 years |
Vulnerable |
hacking, hack, malware, botnet |
5614 |
2 |
| 52 |
 |
Malware Memory Foresnics |
12 years |
Vulnerable |
malware, memory, forensics, hacking, hack |
6060 |
1 |
| 53 |
 |
Dynamic Analysis Of Pdf Shellcode |
12 years |
Keyronie |
malware, pdf, hacking, reverse-engineering |
4649 |
None |
| 54 |
 |
Cuckoo Sandbox Against A Flash Player Exploit |
11 years, 12 months |
Alex-infosec |
hacking, hack, exploit, cuckoo, malware |
4747 |
None |
| 55 |
 |
Analysing A Sample Of A Rogue Antivirus |
11 years, 12 months |
Alex-infosec |
hacking, hack, cockoo, malware, fake, antivirus |
4261 |
None |
| 56 |
 |
Mobile Malware Madness And How To Cap The Mad Hatters |
11 years, 12 months |
tinitee |
hacking, malware, android |
3369 |
None |
| 57 |
 |
One Virus For 3 Differnt Operating Systems |
11 years, 11 months |
_null_ |
GraVitoN, malware, virus, metasploit, armitage, windows 8, linux, osx |
6138 |
1 |
| 58 |
 |
Threat Down - Aug 12 2012 |
11 years, 11 months |
1aN0rmus |
News, TekDefense, Threat Down, doqu, cloud, android, malware, shylock, Iran, Gauss |
4261 |
None |
| 59 |
 |
Tektip Episode 4 - Basic Static Malware Analysis |
11 years, 11 months |
1aN0rmus |
malware, malware analysis, basic, static, PE, md5, strings, dll |
4969 |
None |
| 60 |
 |
Practical Malware Analysis |
11 years, 11 months |
HyBrid |
malware, review, hacking, hack |
5071 |
None |
| 61 |
 |
The Good Hacker:Dismantling Web Malware |
11 years, 11 months |
tinitee |
malware, web-application, penetration-testing |
4027 |
None |
| 62 |
 |
Beacon - Covert Command And Control For Cobalt Strike |
11 years, 10 months |
ArmitageHacker |
beaconing, malware, command and control, post-exploitation, APT, cobalt strike, armitage, C2, DNS, covert communication |
5070 |
None |
| 63 |
 |
Thug And Cuckoo Malware Analysis |
11 years, 9 months |
tinitee |
hacking, hack, malware, anaylsis |
5192 |
None |
| 64 |
 |
Forensic Examinations 8 - Timelines |
11 years, 9 months |
5hark5ter |
digital forensics, computer forensics, malware, ukash, csi, timelines, open source |
4550 |
None |
| 65 |
 |
How To Use Xorsearch |
11 years, 9 months |
tinitee |
hacking, hack, malware |
6148 |
None |
| 66 |
 |
Re-Engineering Android Applications |
11 years, 9 months |
tinitee |
hacking, hack, malware, virus |
3733 |
None |
| 67 |
 |
Death Of Anti-Virus? |
11 years, 8 months |
J4vv4D |
security, infosec, anti virus, malware |
3781 |
None |
| 68 |
 |
Zeus Malware Memory Analysis With Volatility Framework |
11 years, 8 months |
L33T |
zeus, malware, framework, analysis |
15227 |
2 |
| 69 |
 |
Tektip Ep18 - Honeydrive |
11 years, 7 months |
1aN0rmus |
Honeydrive, honeypot, IDS, malware, Mysql, apache, kippo, kippo-graph, honeyd, honeyd-viz, scripts, Dionaea, phplite, Labrea, Tiny Honeypot, IIS Emulator, INetSim, SimH, EtherApe, wireshark, ClamAV, thop, P0f, flawfinder, Automater, Netcat, ssdeep, md5deep, pdftk, flasm, 1aNormus, TekDefense, TekTip |
5595 |
1 |
| 70 |
 |
Setup Automated Malware Analysis - Cuckoo Sandbox On Bt-3 |
11 years, 6 months |
L33T |
hacking, hack, malware, cuckoo, sandbox |
6284 |
1 |
| 71 |
 |
Volatility Spyeye Malware Analysis |
11 years, 5 months |
L33T |
hacking, hack, malware, Spyeye |
3217 |
None |
| 72 |
 |
[Exploit Pack] - Tutorial, How To Use! |
11 years, 4 months |
jsacco |
exploit pack, exploit kit, vulnerability, research, xss, sql, metasploit, core, immunity, security, it security, agent, malware, virus, botnet |
9650 |
None |
| 73 |
 |
Pdf Analysis With Peepdf |
11 years, 4 months |
tinitee |
hacking, hack, pdf, analysis, malware |
4293 |
None |
| 74 |
 |
Parsing Binary File Formats With Powershell |
11 years, 3 months |
tinitee |
powershell, binary, malware, analysis |
4436 |
None |
| 75 |
 |
Joshua Pitts - Backdooring Win32 Portable Executables |
11 years, 2 months |
tinitee |
backdoor, malware, hacking, hack, windows. win32 |
3516 |
None |
| 76 |
 |
Dynamic Malware Analysis |
11 years, 2 months |
tinitee |
dynamic, malware, analysis, hacking, hack |
5345 |
None |
| 77 |
 |
Static Analysis With Ida Pro |
11 years, 2 months |
Alone |
hacking, hack, malware, analysis, static-analysis, IDA-Pro |
5043 |
None |
| 78 |
 |
Malware Hunting With The Sysinternals Tools |
11 years, 2 months |
Alone |
malware, hunting, hacking, hack, stuxnet |
4575 |
None |
| 79 |
 |
Iscanner - Remove Website Malware |
11 years, 2 months |
tinitee |
iscanner, hacking, malware |
4630 |
None |
| 80 |
 |
Ram Scraping Malware |
11 years, 1 month |
pentest |
Ram-scraping-Malware, malware, malware-analysis |
4262 |
None |
| 81 |
 |
James Lyne, Sophos: Anatomy Of An Attack |
11 years, 1 month |
Alone |
hacking, hack, malware, attack |
4465 |
None |
| 82 |
 |
Extracting Badness From A Pdf... In 4 Ways! |
11 years, 1 month |
Alone |
hacking, pdf, analysis, malware, hack |
3518 |
None |
| 83 |
 |
Advanced Forensics Analysis |
11 years |
tinitee |
hacking, hack, malware, pdf, forensics |
3864 |
None |
| 84 |
 |
Tradecraft (5 Of 9) - Post Exploitation With Beacon |
10 years, 9 months |
ArmitageHacker |
tradecraft, cobalt strike, series, beacon, beaconing, malware, low and slow, stealth, evasion, dns, covert communication |
4008 |
None |
| 85 |
 |
Noriben Overview - Behavioral Malware Analysis Script |
10 years, 8 months |
gabriel.pulgar@defpoint.com |
noriben, noriben.py, process monitor, python script, procmon, malware analysis, analysis, malware, overview, behavioral, behavioral analysis, brian baskin, bsides, bsidesdc, beginner |
3652 |
None |
| 86 |
 |
Advanced Ransomware Removal Guide |
10 years, 6 months |
Z___ |
ransomware, malware, removal |
3213 |
None |